HTTP Strict Transport Security or HSTS is a header that instructs a browser not to downgrade a secure https connection to a unsecure HTTP connection for a specified domain.
Something to note:
- HSTS is a standard that browsers (user agents) must adhere to but it is still possible for non-compliant browsers to continue to access a site with the unsecured Http protocol if they don’t adhere to HSTS. The aim of HSTS is to protect vulnerable internet users that are using compliant browsers from man in the middle attacks. Internet Explorer is only complaint in Windows 10.
- HSTS applies to an entire domain. It can not be turned on and off for sections of a website. A website can not be viewed as secure if portions of it transacts in a unsecure manner.
- Once the HSTS header is set all subsequent connections from a compliant browser will be upgraded to connect with HTTPS and it won’t be able to downgrade.
- All connections to the given domain will run with secure http. This includes connections for images, css and scripts.
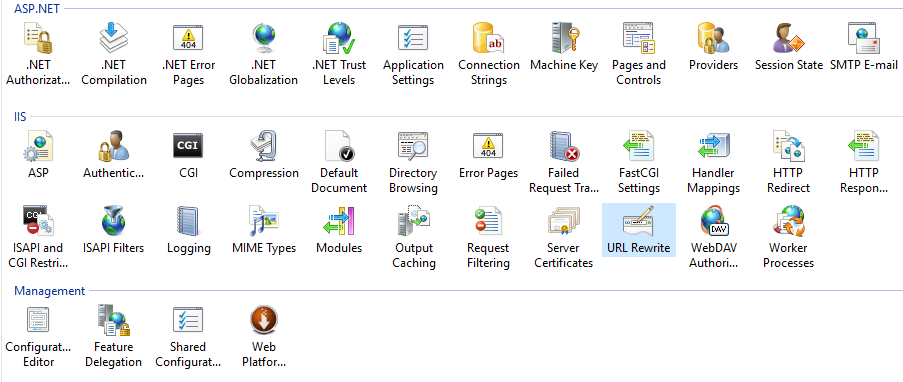
The following solution that I will be provide does require that an additional module called the URL Rewrite module be installed into IIS. Once installed IIS will have an additional icon on the server feature view as you can be seen in the image below. If you are looking for a solution to secure http but whitelist some resource to run unsecured, then click here.
The module is installed, let’s add the rules. Add the following to your web.config.
The rules do the following.
- If a HTTP connection is received it does a redirect to HTTPS protecting the website itself from the server.
- While doing the re-direct it adds the HSTS header. Note the header has a setable life time.
With the combination of these two rules a site will always run secure even with non HSTS compliant user agents.
<system.webServer>
<rewrite>
<rules>
<rule name="HTTP to HTTPS redirect" stopProcessing="true">
<match url="(.*)" />
<conditions>
<add input="{HTTPS}" pattern="off" ignoreCase="true" />
</conditions>
<action type="Redirect" url="https://{HTTP_HOST}/{R:1}"
redirectType="Permanent" />
</rule>
</rules>
<outboundRules>
<rule name="Add Strict-Transport-Security when HTTPS" enabled="true">
<match serverVariable="RESPONSE_Strict_Transport_Security"
pattern=".*" />
<conditions>
<add input="{HTTPS}" pattern="on" ignoreCase="true" />
</conditions>
<action type="Rewrite" value="max-age=31536000" />
</rule>
</outboundRules>
</rewrite>
</system.webServer>
Thank you to Doug Wilson for providing the above rules on stack overflow.
You might also be interested in these posts.
How to disable insecure cipher suits
Enable secure cookies over HTTPS
Remove the IIS version from HTTP response header
Custom Error Pages
Securing website access control