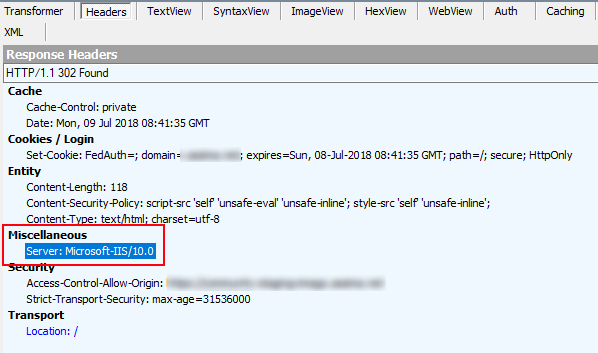
HTTP headers leak technical information to potential attackers about a system. To harden the security of an application you need to disclose as little information about a system as possible. In this post I will show to remove the pesky IIS HTTP server header from responses by modifying the web.config file.
A few months ago I covered how to do HSTS with a url rewrite rule. This post continues on the same topics relating to the security of a web application. By default IIS wants to advertise to the world that it is hosting the website. Here is a good article that explains why its a bad idea to let your web server advertise itself.
How to remove the IIS HTTP server header
In IIS 10+
In IIS 10 a new attribute was added to allow for control in removing the server header.
<system.webServer> <!-- Removed the Server header --> <security> <requestFiltering removeServerHeader="true" /> </security> <system.webServer/>
I have observed that the attribute “removeServerHeader” some times have no affect for some responses even when on IIS 10. See bug in RemoveServerHeader attribute for IIS 10+
I have found that asp.net applications installed on older IIS 8.5 or older web servers breaks if it has the ‘removeServerHeader’ attribute. The asp.net application does not startup until the attribute is removed. No error or exception is thrown or logged in the event viewer. Symptom is that of a white page in the browser and that the application is not responding.
In IIS 7 > IIS 10 (IIS 7, 7.5, 8.0, 8.5)
<system.webServer> <rewrite> <outboundRules rewriteBeforeCache="true"> <rule name="Remove Server header"> <match serverVariable="RESPONSE_Server" pattern=".+" /> <action type="Rewrite" value="" /> </rule> </outboundRules> </rewrite> <system.webServer/>
Removing the X-Powered-By header
Microsoft is always trying to advertise. The next thing to do is to remove the “X-Powered-By” header. This header can be removed either by creating a rewrite rule or by adjusting the custom headers as per in the example below.
<httpProtocol> <customHeaders> <remove name="X-Powered-By" /> </customHeaders> </httpProtocol>
External related posts
Shhh… don’t let your response headers talk too loudly
Removing Unnecessary HTTP Headers in IIS and ASP.NET
Internal related posts
Removing the X-Asp.Net version header
Adjust Asp.net core security headers
How to disable insecure cipher suits.
Securing Http with HSTS in IIS
Enable secure cookies over HTTPS.
Remove the IIS version from HTTP response header
Custom Error Pages
Securing website access control
You may want to tell people the name and location of the file to edit.
thanks, it is working
thanks for saving our day